- Cycore Insights
- Posts
- The $500K Deal That Almost Died Because Nobody Knew Who Answered Security Questions + Security News Round Up for the Week
The $500K Deal That Almost Died Because Nobody Knew Who Answered Security Questions + Security News Round Up for the Week
Your security team just killed another deal. Not through a breach, not through poor controls, but through something far more preventable: undocumented processes that turn routine security questionnaires into weeks-long revenue delays. A recently onboarded customer discovered they were hemorrhaging deals because their security questionnaire response process resembled a game of telephone played across multiple time zones. Technical questions bounced between IT and compliance, financial security inquiries sat in email limbo, and business continuity questions disappeared into Slack black holes.The wake-up call? A $500K deal nearly walked because a simple SOC 2 verification took three weeks to answer.

Happy Thursday!
Welcome to Cycoresecure.com, your go-to partner for transforming security and compliance into effortless processes. Whether you're a startup or a growing tech company, we provide services to tackle your biggest security challenges, freeing you to focus on scaling your business with confidence. Let's secure your future together!
Make sure to follow our Cycore LinkedIn page and subscribe to receive updates on current events, trends, and industry news that matter to you
In Today's Rundown
Let’s dive right in.
You're reading the Cycore Insights newsletter.
Get exclusive coverage of cybersecurity and privacy delivered once a week.
The Cost of Security Process Chaos
Documentation isn't just operational hygiene—it's competitive advantage. When prospective clients send security questionnaires, they're not just evaluating your controls; they're evaluating your organizational maturity. Every delayed response, every "let me check with my team" email, every missed deadline screams operational dysfunction.
Here's what prospects actually see when your security questionnaire process breaks down:
Week 1: Initial confusion about questionnaire ownership signals poor internal coordination
Week 2: Delayed technical responses suggest inadequate security expertise
Week 3: Still waiting for answers indicates systemic organizational problems
By week three, they're not just questioning your security posture—they're questioning whether you can deliver on any commitment.
The Four-Pillar Security Questionnaire Framework
Clear Ownership Architecture: Every questionnaire category needs a designated owner, not a committee. Technical infrastructure questions go to the CISO or designated technical lead. Financial security controls route to the compliance manager. Business continuity inquiries land with operations. No exceptions, no overlap, no confusion.
Notification Process Documentation: The moment a questionnaire arrives, everyone knows their role. The process should be so clear that any team member can execute it flawlessly, whether the primary owner is available or not. Document who gets notified, when responses are due, and what happens if someone's unavailable.
Real-Time Status Visibility: Create a tracking system that shows questionnaire status at a glance. Sales teams need to know whether responses are on track, compliance needs visibility into bottlenecks, and leadership requires assurance that deals aren't stalling in security review purgatory.
Domain Expertise Mapping: Different questionnaire sections require different expertise. Technical questions about encryption and access controls demand deep security knowledge. Business impact questions need operational insight. Compliance inquiries require regulatory understanding. Map these domains to specific individuals with documented backup resources.
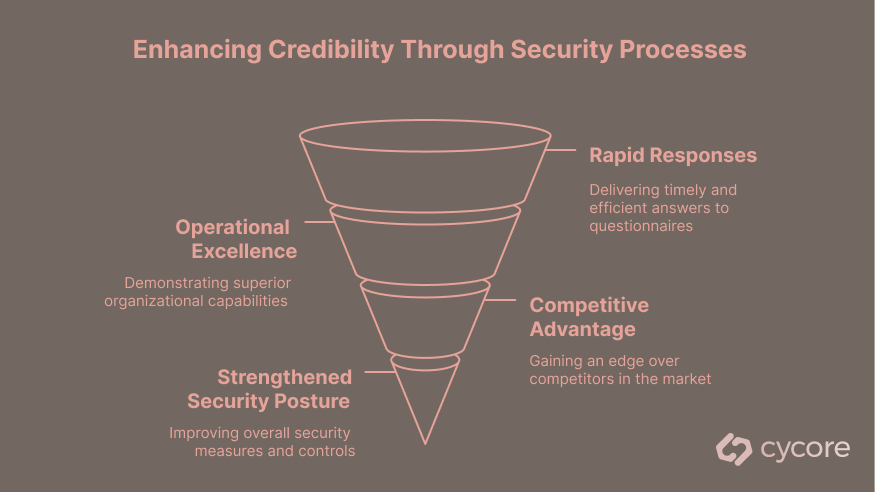
The Credibility Multiplication Effect
Organizations with documented security questionnaire processes don't just respond faster—they demonstrate the systematic thinking that prospects expect from potential partners. Rapid, comprehensive responses signal operational excellence that extends far beyond security controls.I
Consider the competitive advantage: while your competitors struggle through ad-hoc questionnaire responses, your streamlined process delivers comprehensive answers within 48 hours. That responsiveness becomes a differentiator that sales teams can leverage throughout the entire deal cycle.
The documentation discipline required for effective questionnaire management also strengthens your overall security posture. Teams that can efficiently articulate their security controls typically have better-implemented controls in the first place.
Your 7-Day Implementation Sprint
Days 1-2: Audit your last ten security questionnaires. Identify response delays, communication breakdowns, and knowledge gaps. Document every friction point.
Days 3-4: Map questionnaire categories to specific team members. Create backup assignments for each category. Build contact matrices that sales and business development can reference instantly.
Days 5-6: Implement a simple tracking system. This doesn't require enterprise software—a shared spreadsheet with status updates works better than email chains and hoping.
Day 7: Test the process with a mock questionnaire. Time the response cycle, identify remaining bottlenecks, and document the refined workflow.
Bottom Line: Your million-dollar security stack becomes worthless when basic processes aren't documented and followed. Prospects don't care about your sophisticated controls if you can't efficiently communicate them. The organizations winning deals in 2025 understand that security credibility starts with operational excellence.
Security News Roundup
Microsoft, CrowdStrike, Other Cyber Firms Collaborate on Threat Actor Taxonomy: Recently, leading cybersecurity companies, including Microsoft and CrowdStrike, announced a collaborative initiative to standardize the naming conventions for threat groups. This effort aims to eliminate confusion arising from different naming systems that have historically hindered effective threat intelligence sharing. Stakeholders, including Palo Alto Networks and Google’s Mandiant unit, have joined this movement, recognizing the importance of clarity in identifying and responding to threat actors.
Victoria’s Secret Postpones Release of Earnings Due to Cyber Breach Impact: Victoria’s Secret announced it will postpone the release of its fiscal first-quarter earnings report due to the aftermath of a cyberattack. The attack has disrupted access to essential corporate systems needed for financial reporting. While the company disclosed the attack on May 24 and temporarily shut down various corporate systems and its website, it has since restored its web access, but operational recovery remains ongoing.
Ramnit Malware Infections Spike in OT as Evidence Suggests ICS Shift: Honeywell's 2025 Cybersecurity Threat Report highlights a worrying trend in industrial cybersecurity: a significant surge in ransomware and malware attacks, especially targeting operational technology (OT) systems. The report draws attention to the notable increase in such incidents, with over half of the 55 reported cybersecurity events affecting OT in 2024. This trend raises critical concerns about the security posture of industrial organizations amid a growing cyber threat landscape.
Let's Build Trust
Work with us or follow along:
Cycore, builds enterprise-grade security, privacy and compliance programs for the modern organization. Partner with us.
Follow us on LinkedIn for security, privacy & compliance updates!
How else can we help? Feedback? Have a question? Reply to this email.
Know someone who would like this email? Forward it to a friend...
Your security & compliance ally,
Cycore Team